
Avoiding WiFi and Bluetooth Hackers in Your Home | Business and Home Security Solutions | Northeast OhioAvoiding WiFi and Bluetooth Hackers in Your Home

OccupytheWeb on Twitter: "Bluetooth Hacking: How to Control any Mobile Device with Bluetooth Using MultiBlue #bluetoothhacking #bluetooth #cybersecurity #infosec #multiblue #multiblue https://t.co/qYAZXhy1in https://t.co/RIIINIIQ8j" / Twitter


/cdn.vox-cdn.com/uploads/chorus_asset/file/18316592/acastro_190717_1777_bluetooh_0001.jpg)



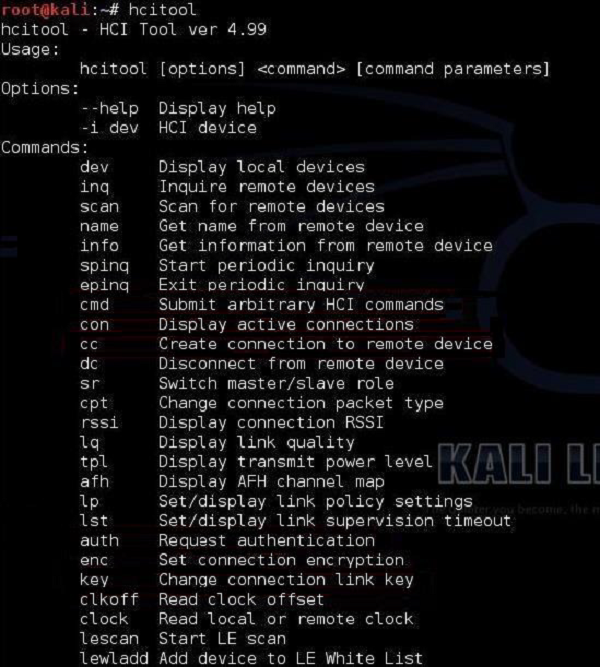
![Snoop on Bluetooth Devices Using Kali Linux [Tutorial] - YouTube Snoop on Bluetooth Devices Using Kali Linux [Tutorial] - YouTube](https://i.ytimg.com/vi/JmQk4Yp9bww/maxresdefault.jpg)

![Identify & Target Bluetooth Devices with Bettercap [Tutorial] - YouTube Identify & Target Bluetooth Devices with Bettercap [Tutorial] - YouTube](https://i.ytimg.com/vi/YDpjGTojByw/maxresdefault.jpg)







![How to Stop Bluetooth Hack on Phone [PDF] | BitVPN Blog How to Stop Bluetooth Hack on Phone [PDF] | BitVPN Blog](http://blog.bitvpn.net/en/wp-content/uploads/2020/03/phone-get-hacked-through-bluetooth.png)